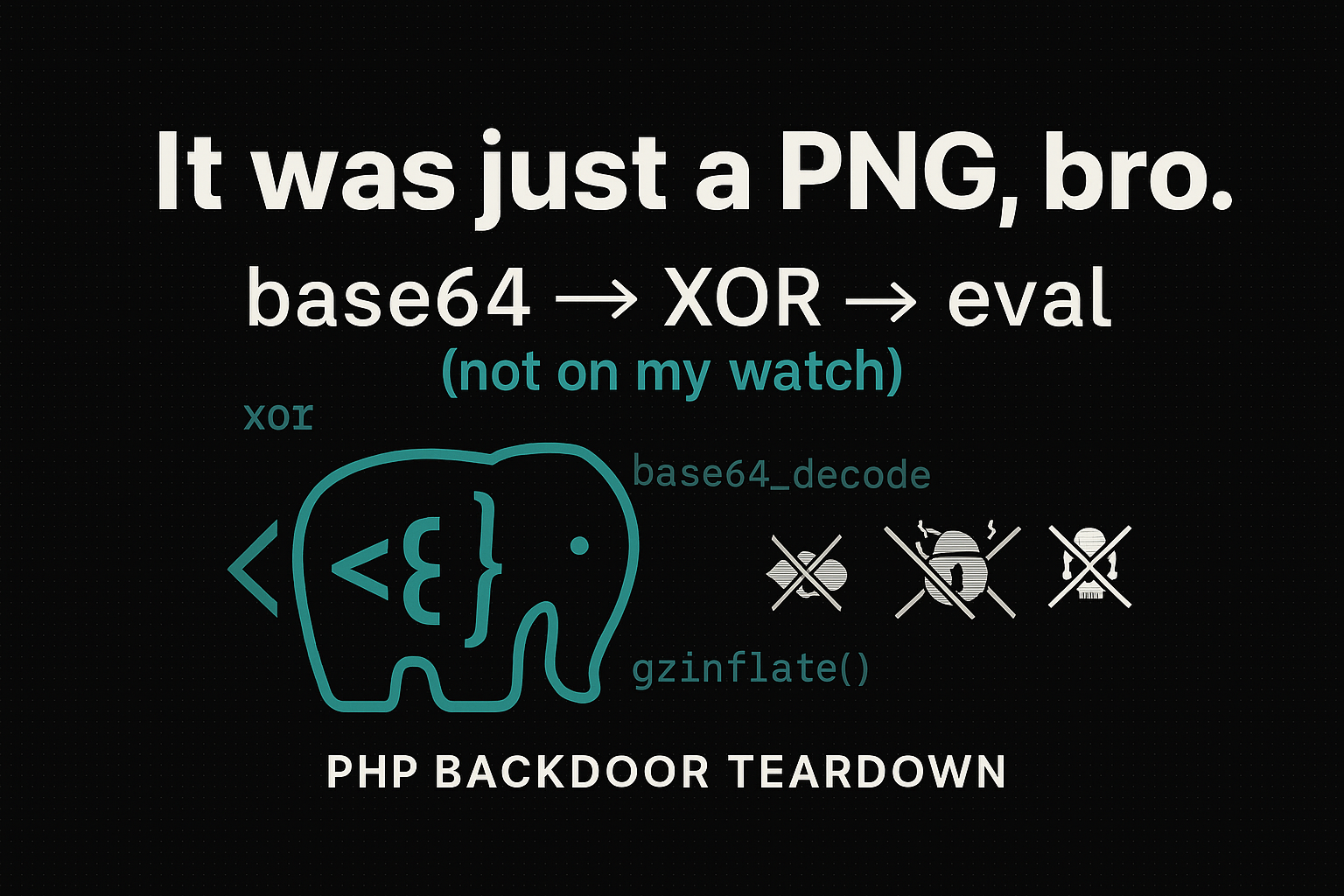
Environmental keying: 16-byte key derived from uptime
This article is 100% defensive and academic. Code examples are neutralized for analysis and detection, they do not show or execute payloads. The goal is to explain the technique, show weaknesses an...